Anticipating Tomorrow’s Threats: A CFO’s Guide to Proactive Cyber Defense

Cyber defense has always been not only an IT issue, but a financial risk.
With the majority of attacks motivated by financial gain and recent incidents increasing in scale and success, fractional CFOs need to prioritize enterprise risk management when working with clients.
And with the consequences of cyber risk exposure and compliance penalties for specific industries and states, the stakes are higher than ever
For fractional CFOs like you, roles are expanding beyond strictly financial-related responsibilities to include knowledge of cybersecurity best practices and the ROI of proactive security measures.
As such, it’s crucial to have strong technology partners you can lean on, like Miles IT. As a nationwide MSP/MSSP with in-depth cybersecurity and compliance expertise, Miles IT helps clients build strong cybersecurity defenses and protect against attacks.
Discover what the 2026 threat landscape means for your clients’ enterprise risk management strategies, and how you can help them make the best financial decisions while maximizing their cyber defense measures.
The Fractional CFO’s Evolving Role in Cyber Defense
In 2026, your fractional CFO role doesn’t only involve counsel on financial strategy, budgeting, and reporting.
It also includes being a proponent for strong cybersecurity as part of an entire enterprise risk management strategy.
According to Gartner, global spending on information security for end users is on track to rise by 12.5% in 2026, with a total amount of $240 billion.
With this rise in cybersecurity spending, today’s fractional CFOs should know that the right technology investments can mitigate financial risks down the line associated with security incidents and fallout costs.
Responsibility for Breaches
Increasingly, CFOs are being tasked with risk management responsibilities as much as CIOs and IT executives are. This shift applies to fractional CFOs as well.
It makes sense—the fractional CFO’s role is about budgeting responsibly and minimizing risks for client organizations.
With cybersecurity risks representing a major threat for organizations of all sizes, you need to work closely with cybersecurity partners and internal security staff to mitigate these threats.
In this way, fractional CFOs become the bridge between IT security and financial strategy.
They’re not only providing consultation on the budget for technologies like firewalls and security training, but are actively involved in quantifying cyber risk exposure to ensure their clients remain financially sound.
Regulatory Pressures
Fractional CFOs and the businesses they serve also face increasing pressure from regulatory bodies like HIPAA, PCI, and SOC, as well as states and their specific requirements.
Failing to comply with the standards required for your clients’ businesses can lead to hefty fines, legal penalties, and reputational damage.
As a major part of clients’ risk management teams, today’s CFOs need to understand the intricacies of compliance standards and how they relate to business systems and processes.
For instance, healthcare organizations or any organization that handles PHI (Patient Healthcare Information) need to safeguard patient data from unauthorized access and follow HIPAA requirements.
To help ensure compliance, practices need to undergo annual risk assessments, create thorough incident response plans, and verify that specific policies and procedures are in place, among other requirements.
If an organization fails to follow HIPAA compliance standards, they may face fines ranging from $100 to $2.1M.
Cybersecurity Budgeting/ROI Shifting to Finance
As Oracle reports, CFOs are progressively becoming more and more involved in cybersecurity discussions and budget planning.
One way that CFOs can contribute is to help identify the value of assets and the appropriate safeguards for them.
Quantifying the potential financial loss if those assets are compromised can also help other executives understand the value of strong cybersecurity and which areas to prioritize first.
Ultimately, fractional CFOs should aim to prove the ROI of cyber defense and how a proactive cybersecurity budget reduces risk and leads to more favorable financial outcomes.
It’s clear that finance, cybersecurity, and compliance are inextricably linked, making it essential for fractional CFOs to champion strong security.
You should expect to be increasingly involved in cybersecurity discussions in 2026 and beyond.
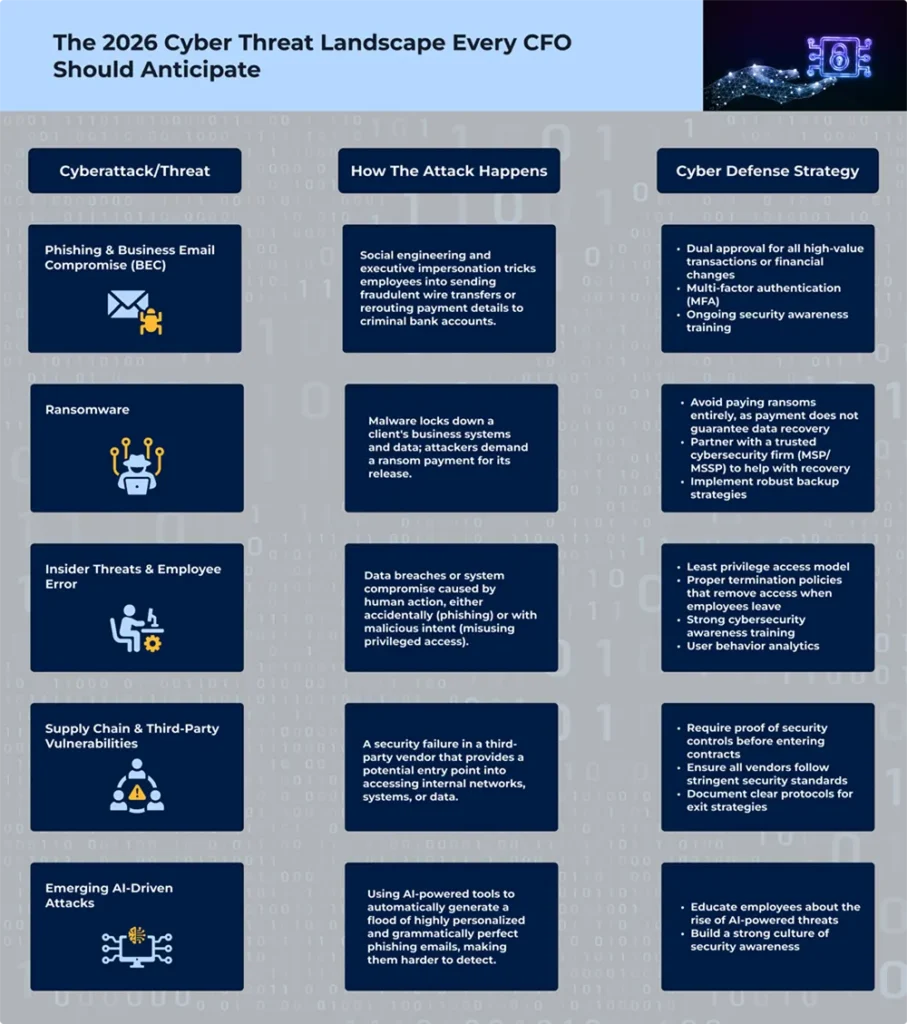
The 2026 Cyber Threat Landscape Every CFO Should Anticipate
With 2026’s threat landscape shifting due to the rise of devastating AI-powered attacks, staying aware and ahead of the newest cyber threats is more important than ever.
And as a fractional CFO, you need to be aware of these changes so you can help your clients implement the strongest proactive measures and ensure proper financial risk management.
Read on to discover the threats you—and your clients—should be aware of.
Sophisticated Phishing Attacks & Business Email Compromise (BEC)
Attackers are moving away from generic phishing emails to orchestrate complex business email compromise (BEC) scams, also called CEO fraud.
These attacks utilize social engineering and involve executive impersonation to convince unwitting employees to send fraudulent wire transfers or reroute payment details to cyber criminal bank accounts.
Major Financial Losses
A single successful fraudulent wire transfer can lead to catastrophic financial consequences.
Consider this: in 2019, a Toyota BEC attack led to a loss of $37 million.
This attack occurred when bad actors contacted a Toyota employee with access to accounting data and financial decision-making.
Using the power of fraudulent impersonation and persuasion, they asked the employee to alter bank account information. Thinking it was a real request, the employee made the updates, which sent the funds directly to the attackers’ account.
How to Prevent BEC Attacks:
Demonstrate the value of ongoing security awareness training to ensure employees are aware of evolving attack methods like BEC.
You’ll also want to encourage your clients to build a security-first company culture, so employees can report anything that seems suspicious.
It’s always better to take extra steps to verify the legitimacy of requests than to fall for an attack.
You can also recommend that your clients implement controls like dual approval for all high-value transactions or financial changes and enforce multi-factor authentication (MFA) across their organization.
Ransomware Targeting SMBs
Ransomware remains a major issue for many businesses. For instance, Verizon’s 2025 Data Breach Investigations Report notes that 44% of all reviewed breaches contained ransomware.
While large enterprises remain targets, SMBs have become prime targets for ransomware, too.
Historically, SMBs have fewer resources to invest in enterprise-caliber cyber defense systems, leaving them more vulnerable to cyberattacks.
Increased Ransom Costs
Although data breach costs decreased as a whole between 2024 and 2025, the average cost of a ransomware attack has actually increased.
Reportedly, ransomware attack costs averaged $4.62 million in 2021; these costs reached $5.08 million in 2025.
This increase in costs is alarming—especially since paying the ransom doesn’t guarantee clients will get their business data back.
We recommend that businesses avoid paying ransoms entirely; instead, they should reach out to a trusted cybersecurity firm to help with next steps after an attack.
Business Continuity Impacts
If ransomware locks down your client’s business systems, they’ll have to deal with more than negotiating the ransom.
They’ll also suffer costs incurred from operational downtime, which differ from business to business. On average, SMBs lose $427 per minute of downtime; that equates to $25,620 per hour.
Beyond that, ransomware attacks can affect your client’s reputation and potentially your reputation, too.
Recovery Costs
The costs don’t end with ransom-related or downtime costs; they also extend to the costs of recovery. These may include forensic measures, system recovery and repair, and PR to handle damage control.
If your clients work with a comprehensive managed service provider (MSP) or managed security services provider (MSSP), they may handle all of these services and include a guarantee for covered labor in the event of a cyberattack or security breach.
Learn how to prevent and recover from ransomware attacks and share with your clients, too.
Tip: Make sure your clients talk to their managed service provider partner about guarantees in the event of an attack, like response time and labor costs, so you’ll have mutual understanding from day one.
Insider Threats & Employee Error
Bruce Schneier once said that “people often represent the weakest link in the security chain.”
Schneier is right; whether malicious or accidental, humans continue to be a primary catalyst of data breaches.
In fact, a 2024 report shows that 83% of organizations reportedly experienced at least one insider threat.
Accidental Errors
The biggest insider threats often come from human mistakes, like falling for a phishing scam.
Bad actors craft believable messages that entice employees to click malicious links or download malware, allowing them to steal credentials or infect their device.
To protect against these risks, ensure your clients have strong cybersecurity awareness training to help employees recognize phishing attempts instead of falling for the traps.
Access Control Gaps
Poor access management creates unnecessary cyber risk exposure by giving employees too much access to privileged systems and information.
Make sure your clients are aware of the least privilege access model and only give employees access to the systems they actually need to do their jobs.
Also, ensure proper termination policies are in place to remove accounts and access when employees leave the company.
Malicious Intent
Unfortunately, not all insider threats are accidental; some employees have malicious intentions.
To protect against these threats, your clients may want to set up user behavior analytics to track unusual logins or access attempts.
The least privilege access model is also helpful in this scenario by preventing employees from having access to confidential data in the first place.
Supply Chain & Third-Party Vulnerabilities
Modern businesses rely on a large number of third-party vendors, from accounting to payment processors.
However, this interconnected nature puts your clients’ organizations at risk if one of their third-party partners experiences a breach or other security event.
Vendor Access Risks
Any vendor that touches your clients’ financial systems (ERP, AR/AP), customer data, or internal network represents a potential attack vector.
A third-party’s security failure exposes your clients’ organizations to cyber risks, too.
As a fractional CFO, this is a risk you must actively mitigate through evaluations or assessments.
Evaluate Vendor Cyber Maturity
A modern cybersecurity governance framework requires the assurance of third-party vendor security.
Your clients must apply the same level of security scrutiny to your vendors as they do to their internal teams.
As a fractional CFO, this applies to any partners you work with, too.
Make sure that you and your clients require proof of security controls, like SOC 2 reports or annual penetration testing results, before entering into a contract.
Plus, ensure that all vendors follow stringent security standards and best practices for access control and data encryption.
You’ll also want to help clients document protocols for exit strategies should you need to leave a vendor relationship.
Emerging AI-Driven Attacks
The rise of artificial intelligence has brought a proliferation of AI-driven threats, making it harder to discern phishing attacks and impersonation scams from real requests.
Automated Phishing
AI-powered tools can automatically generate millions of highly personalized, grammatically perfect phishing emails.
This change makes large-scale attacks easier while making it more difficult for employees to differentiate between phishing attempts and real messages.
Defending Against AI-Driven Attacks
Ensure that your clients educate their employees about the rise in AI-powered threats, from phishing to deepfakes.
You’ll also want to encourage clients to practice double verification methods for any major requests and build a culture of strong security awareness.
The Financial Impact of Poor Cyber Defense
Cyberattacks have far-reaching consequences, especially when it comes to your clients’ finances.
Beyond initial response and downtime costs, businesses can face compliance penalties, cyber insurance premium increases, and more.
Read on for a snapshot of these costs and how your clients could be affected.
Cost Per Breach
According to IBM’s 2025 Cost of a Data Breach Report, the worldwide average cost of a data breach totals $4.4M.
Although this number represents a 9% decrease from 2024, it’s still a staggering amount.
A 2024 study from Microsoft estimates that SMBs spend more than $250,000 on cybersecurity incidents and can pay as much as $7 million.
For some organizations, these costs are so significant that their only alternative is to close the business.
Operational Downtime Cost
Downtime refers to periods when business systems and/or operations are unavailable, leading to a direct loss of revenue, productivity, and business activities.
A security incident affects every area of a business, causing downtime and halting your clients’ ability to provide services and complete work.
According to SolarWinds, smaller businesses face downtime costs of $427 per minute or $25,620 per hour. For larger enterprises, downtime costs average $9,000 per minute or $540,000 per hour.
Plus, if operations grind to a halt, your clients can’t connect with prospects and may lose out on new business.
Reputation Damage Tied to Financial Decline
Security breaches can diminish customer trust and investor confidence, which could directly impact your clients’ financial trajectory.
Though reputational damage is more difficult to quantify, some businesses lose current customers and have trouble attracting new customers.
Over time, this can lead to long-term revenue decline, negatively affecting the business’s ability to continue growing.
Compliance Penalties
Cyberattacks can also result in compliance penalties as a result of inadequate cybersecurity governance and failure to secure sensitive data.
Specific organizations, like public companies, have certain breach notification and security incident requirements they must follow.
Other organizations that fall within the purview of HIPAA or PCI are subject to additional requirements and may receive fines depending on the scope of the incident.
For instance, PCI fines can range from $5,000 to $100,000, and HIPAA fines range from $100 – $2.1 million.
Beyond the fines, businesses must also budget for extensive remediation and credit monitoring mandated after the security event.
Cyber Insurance Premium Increases
Cyber insurance functions similarly to auto insurance; if a major incident (or even a minor incident) occurs, you can expect your premium to increase.
If your clients’ business is affected by a cyber incident, the insurance company will deem them as more risky and increase the premium.
Cyber insurance companies also require comprehensive security controls and security policy enforcement to be in place before issuing policies.
This may include documenting an information security policy, enforcing strong password and MFA requirements, and undergoing a risk assessment to understand the baseline levels of risk.
Where CFOs Lose Money: 4 Hidden Cyber Costs

It can be difficult to quantify the cost of a breach to your clients and help them understand the various associated costs.
To transition to a truly proactive cyber defense budget, make sure you understand these hidden expenses and how they could devastate a business’s financial outlook.
Downtime
Downtime doesn’t just refer to lost sales; it includes the costs incurred when employees are unable to process payments, fulfill orders, or provide services to clients.
To mitigate this threat, encourage clients to take a proactive approach to business continuity planning.
They’ll want to have offsite backups, a robust recovery plan, and detailed processes firmly in place.
Having these elements set up beforehand ensures that your clients can get back up and running as soon as possible, utilizing workarounds in the meantime.
Incident Recovery Costs
Depending on your clients’ partnerships with their MSP or MSSP, they may incur additional incident response costs to cover recovery efforts.
If your clients don’t have a robust IT partnership in place, they may be charged separately for significant security work.
In addition, some businesses may have to replace or upgrade devices or other equipment after a security incident. These costs are often unaccounted for in the yearly budget.
Forensic Investigations
After a major incident, businesses are often required to undergo digital forensics processes.
These efforts identify how the security event happened, determine which data was compromised, and detail the users and organizations that should be notified.
Your clients’ MSP or MSSP may not necessarily handle this as part of their scope of services.
Make sure that your clients know whether their MSSP can complete this work for them. If not, ensure they have the appropriate resources they need to get this important work completed.
Regulatory Fines
If your clients don’t have adequate security policy enforcement, they can face severe financial penalties as a result of regulatory standards like HIPAA and PCI.
Consider the Warby Parker HIPAA violation in 2025. The business was found to violate the HIPAA Security Rule after 200,000 customer records were exposed in 2018, which included ePHI (electronic Protected Health Information).
As a result, Warby Parker had to pay a $1.5 million fine.
Beyond the fines themselves, companies may also be responsible for extensive credit monitoring and recovery programs.
The top hidden cyber costs, in summary:
- Extended periods of downtime due to lost sales and productivity
- Incident recovery costs to resume operations and restore devices
- Digital forensics investigations after a cyber incident
- Regulatory fines from violating standards like HIPAA and PCI
Proactive Cyber Defense: A Strategic Framework for Fractional CFOs
As a fractional CFO, your job is to guide clients toward financial stability and strategic growth.
The following framework covers an example of a high-level strategy you should follow as you work with clients.
1. Strategically Assess Client Cyber Maturity
The first step in a strategic cyber defense framework is to create a baseline of the client’s current cyber risk exposure.
As the counsel for your client’s financial health, you’ll want to transition them from a vague sense of risk to an actionable understanding of their vulnerabilities.
Risk Assessment
Partner with a trusted cybersecurity organization to perform a risk assessment, going beyond a simple IT checklist.
The partner should provide ranked results based on likelihood and severity of the risk occurring, along with recommendations for improvement.
This level of scrutiny helps integrate findings directly into your financial risk management strategy and understand exactly what threats your clients face.
Vendor Risk Assessments
Your client’s security is only as strong as its weakest vendor.
A modern enterprise risk management strategy requires you to hold all third-party providers who handle sensitive data (financial, customer, or internal) to the same high security standards as internal teams.
Require proof of cybersecurity governance in the form of SOC 2 reports, pen test results, or audits before signing contracts.
Review Security Controls & Compliance Requirements
Depending on your client’s industry, they may be responsible for adhering to specific compliance requirements like HIPAA, PCI, and CMMC.
Make sure those requirements are documented upfront so you understand what regulations need to be followed.
From there, you’ll want to confirm that current security controls and security policy enforcement measures directly align with those standards.
2. Build a Financially Proactive Cyber Budget
Next, you’ll want to help your clients create a forward-thinking budget to maximize security coverage and minimize gaps.
Proactive vs. Reactive IT Spending
Encourage your clients to shift from unpredictable reactive IT spending to predictable proactive spending.
An IT services provider can help implement proactive measures that include security protection, ongoing maintenance, and 24/7 monitoring to ensure nothing gets missed.
In the long run, predictable monthly costs are more budget-conscious than inflated emergency spending.
Managed vs. Internal Security
Work with your clients to evaluate the cost-benefit analysis of outsourcing 24/7 security vs. creating a 24/7 internal security team.
Building an internal security team incurs a variety of recruiting and retention costs that you’ll avoid by working with an outside provider. Often, it’s more cost-effective to work with an MSSP for consistent, 24/7 monitoring.
An MSSP will also have access to enterprise-level security tools, giving your clients enterprise-level security at a fraction of the cost.
Zero Trust Principles
Encourage your client to implement security measures like access control and MFA to close access gaps.
These types of security initiatives ensure employees are only given the exact permissions that they need, which help prevent insider threats.
3. Implement Advanced Threat Monitoring
Managed Detection & Response (MDR) is crucial to minimize the impacts of security incidents for your clients.
Focus on services that guarantee rapid detection and minimize extended downtime.
24/7 Oversight
Encourage your clients to have 24/7 monitoring; an MSP or MSSP can typically provide this type of comprehensive service.
Ongoing monitoring ensures rapid response, drastically reducing the chances of extended downtime periods or undetected security incidents.
Comprehensive Security Information Event Monitoring (SIEM)
The right MSP or MSSP will usually include SIEM services as part of their packages.
SIEM is essential for collecting and analyzing security log and event data across all devices and applications. It can identify anomalies and patterns as they happen, making it easier to detect suspicious activity.
SIEM is one of the most important steps your clients can take; it enables better detection and alerts, driving better understanding in the event of an incident.
Compliance standards will dictate retention policies related to these tools, so encourage your clients to consult with compliance experts as necessary.
4. Strengthen Employee Training & Culture
Remember that employees are the weakest link in any security program.
For fractional CFOs, acknowledging and addressing this issue is a crucial part of enterprise risk management.
With the right training, your clients’ employees can be an effective part of your cyber defense strategy.
Focus on Human Error
Training staff members to avoid clicking unknown links and report suspicious activity is an indispensable part of cyber risk management.
If your clients remain unconvinced, share case studies that detail the proliferation of cyberattacks caused by human error or insider threats.
Build a Security-First Culture
Encourage your clients to build a security-centric culture at their organizations.
If employees feel comfortable questioning the legitimacy of requests, the entire organization will be more secure.
Implement dual-verification policies for financial transactions to defend against business email compromise and deepfake attacks.
5. Test Defenses Annually
Strategic testing is not optional; it’s a non-negotiable for your clients to ensure they meet current enterprise risk management requirements.
By actively testing their defenses, you’ll validate the effectiveness of proactive security investments.
Your clients will want to continue to complete these tests on a regular basis; some organizations may need to do this to align with various compliance standards.
Penetration Testing
Third-party penetration testing gives your clients an objective, real-world understanding of their system weaknesses by simulating a determined, malicious attack.
A penetration test takes a more in-depth approach than a vulnerability scan does. It involves human beings actively searching for vulnerabilities to see if the tools missed anything.
Make sure results quantify the financial risks to ensure highest-impact vulnerabilities are prioritized first.
Tabletop Exercises
Empower your client to work with third-party experts to conduct tabletop tests, which examine their team’s ability to respond to and handle a crisis, like an insider threat or compromised account.
These tests also identify critical gaps in technical systems, communication, decision making, and financial reporting during an emergency.
For instance, what would your client do if there was a critical security alert at 3 AM? Are appropriate chains of communication established to let the right teams know?
Experts can also add more variables to the simulation to make sure all scenarios are accounted for.
By simulating security events, your clients can reduce the time it takes to contain an actual attack and get back up and running.
This reduction in downtime translates to a huge savings on operational downtime costs, mitigating financial risk management exposure.
Fractional CFO’s Cyber Defense Checklist
Use this checklist as a reference point for your clients’ cybersecurity governance position.
Strong security policy enforcement will help build greater defenses against emerging threats in 2026.
- Incident Response Plan: Is there a clear, approved Incident Response Plan in place?
- Budget Alignment: Do cybersecurity investments demonstrate a clear ROI?
- Third-Party Vendor Controls: Are there strong vendor agreements in place? Have vendor and third-party risk assessments been completed?
- Backup Strategy: Is there a strong immutable backup solution in place? Is there a disaster recovery & business continuity plan?
- Incident Response Guarantee: Does the client’s chosen MSP or MSSP partner guarantee fast response and 24/7 oversight?
- Access Controls: Is the zero trust/least privilege principle enforced across the organization to manage cyber risk exposure?
- Compliance Alignment: Is the client aware of all regulations for their industry and state? Do current security controls and processes align with these requirements?
How to Evaluate a Cybersecurity Partner as a CFO
In your role as a fractional CFO, clients will look to you to not only guide their financial and strategic decisions, but also to help evaluate and choose the best partners to strengthen their cyber defenses.
Your reputation hinges on helping them select trustworthy, knowledgeable partners who provide the right level of managed IT support and cybersecurity expertise.
Consider the following criteria when helping your clients evaluate cybersecurity partners.
Top Criteria When Evaluating Cybersecurity Partners
Deliver Measurable ROI
Your clients expect you to understand how specific security measures will impact their budget—and they expect you to provide those answers transparently.
Make sure your cybersecurity partner provides clear, understandable pricing and makes it easy to understand their services.
You’ll also want measurable ROI from your security partner in terms of provided services and risk reduction.
Understand Business & Technology
Working with technical experts is a must, but any IT and cybersecurity partner also needs to have a strong understanding of common business processes and best practices.
Verify that your partners have a deep understanding of the business landscape.
Have they worked with your clients’ industries before? Do they truly understand the cost of downtime for SMBs? Are they on the pulse of the business community as well as the latest technology shifts?
You’ll want a partner that not only understands technical details, but also knows how technology fits into the broader organizational picture.
Provide Governance, Risk, & Compliance Advisory Services
Any cybersecurity partner must have a strong understanding of compliance regulations and how they relate to your clients’ businesses.
These requirements include HIPAA, PCI, CMMC, NIST 800-171, SOC 2, and SOX, in addition to any other state or industry-specific requirements.
Each requirement has specific rules detailing data handling, breach notifications, and security frameworks. Your cybersecurity partner should have resources and knowledge surrounding these areas to help ensure compliance for your clients.
Ask potential partners to provide industry-specific references so you can see whether they’ve worked with your clients’ industries before.
Offer 24/7 Monitoring and Incident Response
If your clients’ systems stop operating or if they experience a cyberattack, they need to know that someone is available on the front lines, ready to assist.
The right cybersecurity partner will provide 24/7 monitoring and thorough incident response, no matter what time of day it is.
Having a reliable partner overseeing your clients’ systems helps minimize downtime, protect against catastrophic security incidents, and saves costs related to both.
Make sure any cybersecurity partner can provide comprehensive support at any time of day or night.
Provide Ongoing Proactive Maintenance
Proactive maintenance is key to reducing costs in the long run and building a strong cyber defense for your clients. Proactive fixes result in predictable monthly costs, updated infrastructure, and peace of mind.
On the other hand, reactive fixes are usually unpredictable, expensive, and stressful. Often, they’re the result of an emergency, like business downtime or a cyberattack.
Ensure your provider offers proactive services related to IT maintenance and upkeep and cybersecurity. With threats constantly evolving and cyber risk exposure changing, you’ll want a partner that helps your clients stay ahead of those changes—and ahead of bad actors, too.
Top criteria for evaluating cybersecurity partners, in summary:
- Deliver measurable ROI
- Understand business & technology
- Provide governance, risk, & compliance guidance
- Offer 24/7 monitoring and incident response
- Provide ongoing proactive maintenance
Red Flags When Evaluating Cybersecurity Partners
Stay aware of these red flags when assessing potential cybersecurity partners, as these can be signs that a provider will not be able to adequately protect your clients’ businesses.
Unresponsiveness/No 24/7 Availability
If a cybersecurity incident occurs, your clients’ MSSP needs to jump into action immediately.
Cybersecurity providers should provide 24/7/365 availability to respond to cyber incidents and emergency IT requests.
Make sure it’s easy to reach the partner and they reply quickly to your client’s requests.
Negative Reviews/Reputation
Work with your clients to carefully evaluate a provider’s reputation and reviews. Prioritize well-established cybersecurity partners with clear, honest reviews and a strong history of helping similar companies.
Talking to other businesses can also deepen your understanding of the landscape and the best providers to work with.
Unclear Coverage Information
Transparency is key when entering any partnership.
Ensure the provider offers clear, easily understandable information about covered items and service plans.
If coverage options appear vague and difficult to understand, the partner may not be a good fit for your clients.
Industry Unfamiliarity
Ideally, your clients should work with cybersecurity experts who are working with businesses in their industry.
This is especially helpful for organizations in regulated industries, like healthcare and finance, because they often need to align with specific compliance standards like HIPAA and PCI.
Choose trusted industry experts that already understand best practices for enterprise risk management and how that applies to your client’s vertical and business systems.
Why Miles IT Is the Trusted Cyber Defense Partner for CFOs
With 25+ years of IT and cybersecurity experience, Miles IT is trusted by many businesses across a variety of industries.
As a nationwide MSP with local support across the US and internationally, we provide 24/7/365 IT assistance, with an always-available SOC.
Rapid response is incredibly important to us, as shown in our slogan, “You Request, We Respond, It Gets Done!” We’re dedicated to providing fast, high-quality support to our clients at any time of day or night.
Our cybersecurity services include in-depth proactive services, like monitoring, maintenance, and risk assessments, in addition to comprehensive incident response services.
We also offer governance, risk, and compliance advisory services, helping clients prepare for audits, and helping to ensure their processes and systems align with regulations like HIPAA, PCI, CMMC, NIST 800-171, SOC 2, and SOX.
Transparency and clarity is essential to us, too; we focus on providing proven results and visible success metrics to our customers.
Interested in helping your clients improve their security posture?
Schedule a consultation with Miles IT today.
Final Thought
As a fractional CFO, your role extends beyond basic financial planning; it involves a knowledge of enterprise risk management and how you can best set your clients up for success.
With the devastating financial costs and negative reputational repercussions from cyberattacks, you’ll want to ensure your clients have the best protection possible.
Cyber threats are evolving every day, and they require proactive planning and maintenance to make sure your clients aren’t swept up in the frenzy. Done right, proactive cyber defense becomes a strategic advantage for businesses.
Encourage your clients to take a proactive stance to cybersecurity so they can protect their business, data, customers, and future.
Questions about cyber risk exposure in today’s landscape? Book a call with a security expert.
